在 CentOS 8 上,最新的 OpenVPN(截至撰写本文时的版本 2.4.8)由 EPEL 存储库提供。
# dnf info openvpn
Name : openvpn
Version : 2.4.8
Release : 1.el8
Arch : x86_64
Size : 540 k
Source : openvpn-2.4.8-1.el8.src.rpm
Repo : epel
Summary : A full-featured SSL VPN solution
URL : https://community.openvpn.net/
License : GPLv2
...要在 CentOS 8 上安装 OpenVPN 客户端,您需要安装 EPEL 存储库(如果尚未安装);
dnf install epel-release然后可以通过执行命令安装OpenVPN客户端;
dnf install openvpn在 CentOS 8 上配置 OpenVPN 客户端
为了能够连接到 OpenVPN 服务器,您需要创建包含 CA 证书、客户端服务器证书和密钥的客户端配置文件。比较方便的是这个配置文件一般可以在服务器端直接导出。
生成密钥后,将它们复制到客户端并记下它们的存储路径。
您还需要将 HMAC 密钥和 CA 证书复制到客户端。
[root@iZ2ze2jeancylpl40jff7wZ client]# ls
borun_openvpn_remote_access_l3.ovpnOpenVPN 客户端配置文件现已准备就绪。
然后,您可以按需连接到 OpenVPN 服务器,或者配置您的服务器以在系统重新启动时建立 VPN 配置文件。
要按需连接,只需使用 openvpn 命令即可;
sudo openvpn client.ovpn
或者
sudo openvpn --config client.ovpn如果与 OpenVPN 服务器的连接成功,您应该会看到一个 Initialization Sequence Completed.
...
[root@iZ2ze2jeancylpl40jff7wZ client]# openvpn borun_openvpn_remote_access_l3.ovpn
Fri Nov 17 10:03:43 2023 OpenVPN 2.4.12 x86_64-redhat-linux-gnu [SSL (OpenSSL)] [LZO] [LZ4] [EPOLL] [PKCS11] [MH/PKTINFO] [AEAD] built on Mar 17 2022
Fri Nov 17 10:03:43 2023 library versions: OpenSSL 1.1.1g FIPS 21 Apr 2020, LZO 2.08
Enter Auth Username: userchen
Enter Auth Password: *******
Fri Nov 17 10:03:54 2023 WARNING: No server certificate verification method has been enabled. See http://openvpn.net/howto.html#mitm for more info.
Fri Nov 17 10:03:55 2023 TCP/UDP: Preserving recently used remote address: [AF_INET]61.52.96.252:1195
Fri Nov 17 10:03:55 2023 Socket Buffers: R=[212992->212992] S=[212992->212992]
Fri Nov 17 10:03:55 2023 UDP link local: (not bound)
Fri Nov 17 10:03:55 2023 UDP link remote: [AF_INET]61.52.96.252:1195
Fri Nov 17 10:03:55 2023 TLS: Initial packet from [AF_INET]61.52.96.252:1195, sid=00555eae 1b6d9dc2
Fri Nov 17 10:03:55 2023 VERIFY OK: depth=0, CN=vpn458425026.softether.net, O=vpn458425026.softether.net, OU=vpn458425026.softether.net, C=US
Fri Nov 17 10:03:55 2023 Control Channel: TLSv1.2, cipher TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384, 2048 bit RSA
Fri Nov 17 10:03:55 2023 [vpn458425026.softether.net] Peer Connection Initiated with [AF_INET]61.52.96.252:1195
Fri Nov 17 10:03:56 2023 SENT CONTROL [vpn458425026.softether.net]: 'PUSH_REQUEST' (status=1)
Fri Nov 17 10:03:56 2023 PUSH: Received control message: 'PUSH_REPLY,ping 3,ping-restart 10,ifconfig 192.168.30.13 192.168.30.14,dhcp-option DNS 192.168.30.1,route-gateway 192.168.30.14,redirect-gateway def1'
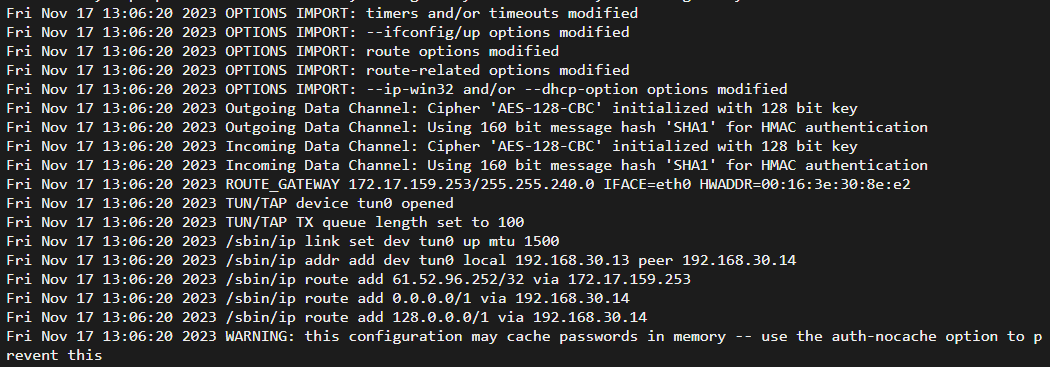
Fri Nov 17 10:03:56 2023 OPTIONS IMPORT: timers and/or timeouts modified
Fri Nov 17 10:03:56 2023 OPTIONS IMPORT: --ifconfig/up options modified
Fri Nov 17 10:03:56 2023 OPTIONS IMPORT: route options modified
Fri Nov 17 10:03:56 2023 OPTIONS IMPORT: route-related options modified
Fri Nov 17 10:03:56 2023 OPTIONS IMPORT: --ip-win32 and/or --dhcp-option options modified
Fri Nov 17 10:03:56 2023 Outgoing Data Channel: Cipher 'AES-128-CBC' initialized with 128 bit key
Fri Nov 17 10:03:56 2023 Outgoing Data Channel: Using 160 bit message hash 'SHA1' for HMAC authentication
Fri Nov 17 10:03:56 2023 Incoming Data Channel: Cipher 'AES-128-CBC' initialized with 128 bit key
Fri Nov 17 10:03:56 2023 Incoming Data Channel: Using 160 bit message hash 'SHA1' for HMAC authentication
Fri Nov 17 10:03:56 2023 ROUTE_GATEWAY 172.17.159.253/255.255.240.0 IFACE=eth0 HWADDR=00:16:3e:30:8e:e2
Fri Nov 17 10:03:56 2023 TUN/TAP device tun0 opened
Fri Nov 17 10:03:56 2023 TUN/TAP TX queue length set to 100
Fri Nov 17 10:03:56 2023 /sbin/ip link set dev tun0 up mtu 1500
Fri Nov 17 10:03:56 2023 /sbin/ip addr add dev tun0 local 192.168.30.13 peer 192.168.30.14
Fri Nov 17 10:03:56 2023 /sbin/ip route add 61.52.96.252/32 via 172.17.159.253
RTNETLINK answers: File exists
Fri Nov 17 10:03:56 2023 ERROR: Linux route add command failed: external program exited with error status: 2
Fri Nov 17 10:03:56 2023 /sbin/ip route add 0.0.0.0/1 via 192.168.30.14
Fri Nov 17 10:03:56 2023 /sbin/ip route add 128.0.0.0/1 via 192.168.30.14
Fri Nov 17 10:03:56 2023 WARNING: this configuration may cache passwords in memory -- use the auth-nocache option to prevent this
Fri Nov 17 10:03:56 2023 Initialization Sequence Completed检查IP地址;
[root@iZ2ze2jeancylpl40jff7wZ ~]# ip add show tun0
7: tun0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UNKNOWN group default qlen 100
link/none
inet 192.168.30.13 peer 192.168.30.14/32 scope global tun0
valid_lft forever preferred_lft forever
inet6 fe80::a9f2:6778:df43:14c5/64 scope link stable-privacy
valid_lft forever preferred_lft forever测试两个远程服务器之间的连通性;
[root@iZ2ze2jeancylpl40jff7wZ ~]# ping 192.168.1.110
PING 192.168.1.110 (192.168.1.110) 56(84) bytes of data.
64 bytes from 192.168.1.110: icmp_seq=1 ttl=127 time=20.9 ms
64 bytes from 192.168.1.110: icmp_seq=2 ttl=127 time=20.5 ms
64 bytes from 192.168.1.110: icmp_seq=3 ttl=127 time=20.10 ms
^C
--- 192.168.1.110 ping statistics ---
3 packets transmitted, 3 received, 0% packet loss, time 5ms
rtt min/avg/max/mdev = 20.505/20.805/20.982/0.243 ms现在应该能够根据服务器的路由设置访问你的内网。
